Profile

JESUFEMI E. DADA
Cybersecurity professional | ISC2 Certified in Cybersecurity (CC) | IoT/OT Security | Cloud Security | SOC | Member, Chartered Institute of Information Security (CIISec.)
PROFESSIONAL PROFILE
About
A driven and results-oriented MSc Cybersecurity student at Keele University, ISC² Certified in Cybersecurity (CC) and a CIISec member, I am deeply committed to understanding and reducing the human and organisational factors that drive cyber risk, and to applying security best practice in real-world environments.I bring a strong foundation across defence-in-depth, secure systems design, and incident response, with a track record of analytical problem-solving, rigorous research, and clear communication to both technical and non-technical stakeholders.Led an independent phishing behaviour study conducted under strict ethical considerations in line with GDPR and the BPS Code of Human Research Ethics, exploring the psychological and behavioural patterns behind user susceptibility to social engineering attacks, and translating findings into a targeted phishing awareness training programme designed to reduce real-world vulnerability.Also combines this behavioural insight with hands-on technical expertise in secure IoT system simulation, TLS-encrypted communications, JWT authentication, and real-time intrusion detection.Brings practical experience in incident response and IT support, with a proven ability to analyse complex security challenges, identify root causes, and act decisively under pressure while maintaining a structured, research-driven approach to problem-solving.
Projects
01
02
03
Secure Smart Hotel IoT Security System Simulation: Implementing Defence in Depth Through Device-Level JWT Authentication and Real-Time Intrusion Detection
|Personal Project | February 2026
A Python-based IoT security simulation demonstrating defence in depth across door access control, camera command channels, and HVAC systems,using MQTT with TLS encryption and JWT authentication at device controller level.Three security-critical components, door access control, cameras, and HVAC are each simulated as Python scripts communicating over a real MQTT broker. Rather than trusting the MQTT broker as the main security boundary, every controller (ACU) enforces JWT authentication at device level, blocking unauthorised commands even from attackers with valid broker credentials.A lightweight IoT IDS monitors all channels simultaneously, publishing real-time alerts to a Node-RED dashboard, providing live visual visibility of every device status, access event, and security alert in one place. This ensures attacks are not just blocked but detected, alerted, and visible in real time. Together, these layers address a gap most commercial IoT deployments leave entirely unguarded.
Cloud-Native Medical Imaging Platform on AWS with Secure Scalable Architecture.
|Module Project | March 2026
Designed and presented a cloud-native medical imaging web service application as part of my MSc Cybersecurity module in Data Management and Cloud Technologies. The project involved full architectural design, AWS service selection with justified trade-off analysis, and delivery through a structured slide deck and video presentation.It explored IaaS, PaaS, and SaaS models using real-world cloud provider examples and applied them to a medical imaging context. The system architecture was designed across five layers, covering network security, application, data storage, big data analytics, and security management.The design used AWS VPC, CloudFront, and Shield at the network layer; API Gateway, Application Load Balancer, and Auto Scaling EC2 at the application layer; and S3, RDS PostgreSQL, and DynamoDB for storage and metadata management. It also integrated AWS Glue, Redshift, and Lambda for analytics and stream processing, alongside IAM, KMS, and CloudTrail for secure access, encryption, and audit logging. I also completed five AWS Academy Cloud Foundations modules, achieving 100% in all of them.
Professional
Certifications
01
Certified in Cybersecurity (CC) | ISC2
Issued: March 2026

Credential ID: 3578317
02
Chartered Institute of Information Security (CIISec)
Issued: October 2025
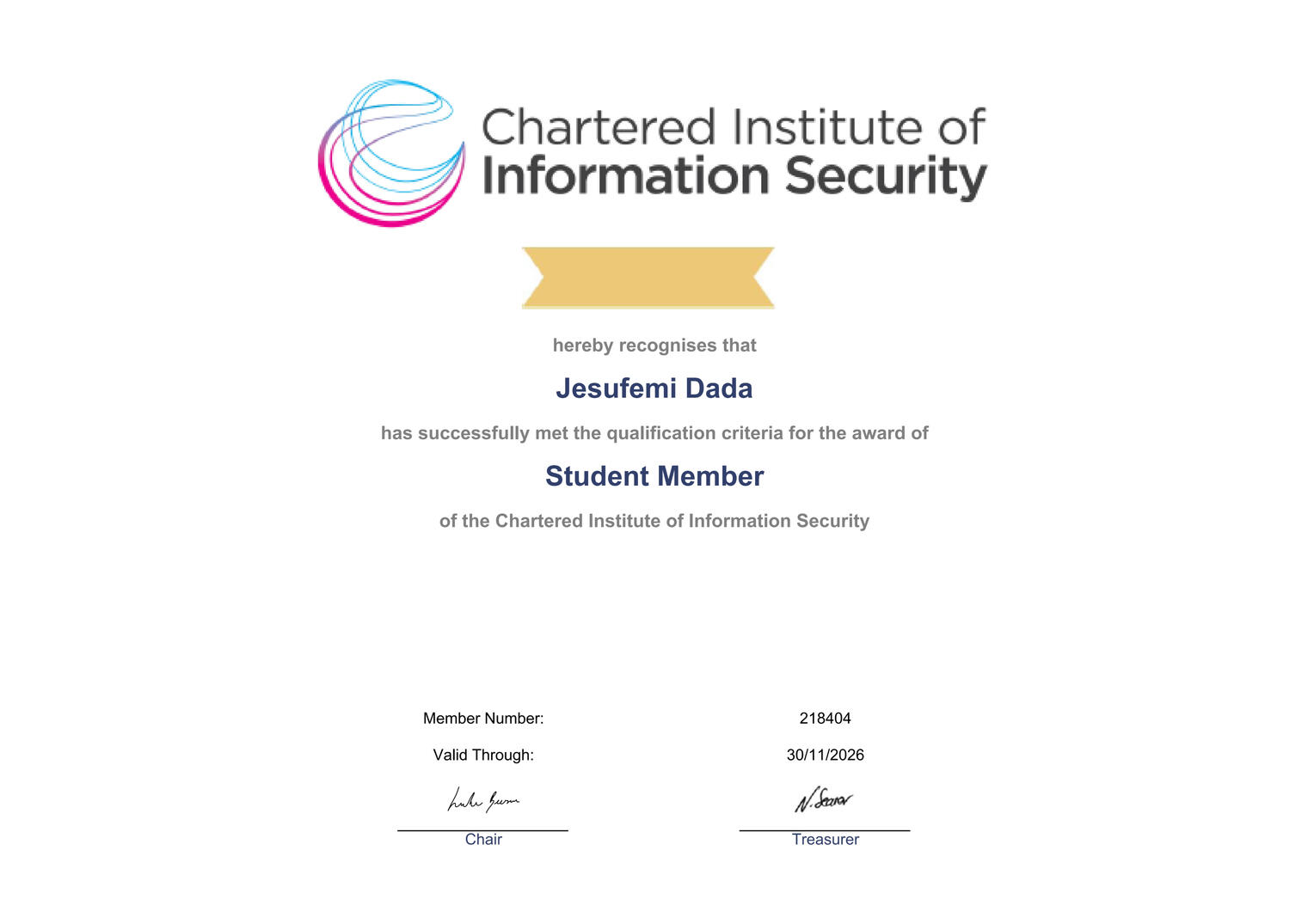
Membership Number:218404
Professional
Engagements
National Cyber Security Show | NEC Birmingham, England, UK
Cyber Solution Theatre | 28th-30th April, 2026



Attended the Cyber Solutions Theatre at the National Cyber Security Show 2026, and it was a highly valuable experience. As someone who enjoys attending cybersecurity conferences and events to listen to employers, business owners, and professionals discuss current trends and challenges in cybersecurity, this was a great opportunity to gain practical insight. The sessions covered a range of key topics, including compliance across frameworks, deepfake-enabled threats, browser and workspace security, proactive application security, MDR, and supply chain risk. What stood out most was how these challenges are being addressed in real-world environments.As someone building a career in cybersecurity, I found the discussions around security foundations, AI-driven threats, continuous validation in AppSec, and shared supply chain risk particularly relevant. They reinforced the idea that effective security goes beyond tools, requiring clear thinking, practical controls, and adaptability.I also really valued the opportunity to network with experienced professionals. Those conversations provided useful insight into industry expectations, key skills, and the direction I want to keep pursuing in cybersecurity.
NDC Manchester 2025 – AI & Security | Manchester, England, UK
Crew Member & Volunteer | December, 2025



Volunteered as a Crew Member at NDC Manchester 2025 – an AI & Cybersecurity conference featuring deep-dive, multi-track sessions on secure coding, AI red-teaming, supply chain security, data-streaming security, and building secure infrastructure for AI agents.
Supported smooth day-to-day operations by assisting with speaker and attendee check-in, room setup and turnaround, session timing, crowd flow, and on-site guidance. This helped ensure sessions ran on schedule and participants had a positive and seamless conference experience.
As someone who actively attends cybersecurity events to learn from employers, business owners, and industry professionals about current trends and real-world challenges, this was a valuable opportunity to both contribute and gain insight into the field.
Contact
I am currently open to new opportunities and would love to discuss how my skills can help your team. If you’re looking for a dedicated professional to bring your next project to life, please reach out below
Thank you
Thank you for visiting!I appreciate you taking the time to review my work. If you've sent a message, I will get back to you within 24–48 hours. I look forward to the possibility of working together.


